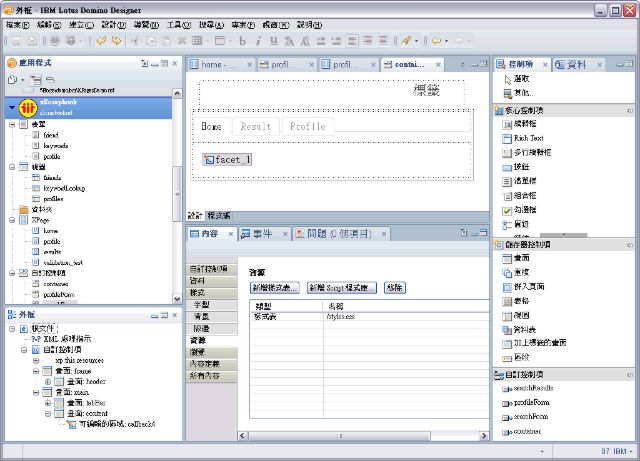
One popular entry in this blog is "
Fixing a Notes database" Which provides a small MS-Windows command file to clean-up a notes database when your server or client isn't running. While it works very well, it has two caveats: For one on a MS-Windows system you might encounter severe fragmentation on your drive (thank NTFS for that), two it is MS-Windows only.
For the first problem you have three possible actions short of moving to an OS with less fragmentation problems for large files:
- use Windows build in Defrag
- use DominoDefrag on OpenNTF
- use Defrag.nsf from our Australian Business Partner Preemptive Consulting
I haven't used the later two (since they were not available when I left the MS-Windows camp). Both apparently use the Windows defrag API while defrag.nsf also does some clever things around size and index allocation (so they claim). I'll report on my experiences soon.
So where does that leave a Linux user? There is a
lot of discussion around the need, or the lack thereof for Linux defragmentation, so I leave that to the individual reader. It isn't as easy on Linux, since you have a choice of file systems: EXT3/4, Raiser, JFS, XFS, ZFS etc. (I run JFS). However having that little script mentioned in the post above comes in handy, so here we go:
Notes Edition
/opt/ibm/lotus/notes/fixup -L -F -Y $1
/opt/ibm/lotus/notes/compact -D -c -i -n -v -ZU $1
/opt/ibm/lotus/notes/updall -R $1
/opt/ibm/lotus/notes/updall -X $1
Domino Edition
/opt/ibm/domino/bin/fixup -L -F -Y $1
/opt/ibm/domino/bin/compact -D -c -i -n -v -ZU $1
/opt/ibm/domino/bin/updall -R $1
/opt/ibm/domino/bin/updall -X $1
You might need to adjust the path to the executables if you have installed them elsewhere. Create a file in /usr/local/bin with the above content and make it executable (you don't need a file extension):
gksu gedit /usr/local/bin/fixnotesdb
sudo chmod +x /usr/local/bin/fixnotesdb
Make sure that your notes.ini contains
CREATE_R85_DATABASES=1 or
CREATE_R9_DATABASES=1
As usual: YMMV.
Update: There is a
Mac version too